Introduction to Supply Chain Digital Risk
Over the last two decades businesses around the world have enjoyed unprecedented opportunities, owing to a large extent to the many benefits of globalisation, new digital technologies, and the resulting interconnected supply chains. As companies have grown, their dependencies on their suppliers have increased which has led to tighter and more collaborative relationships. However, rewards are balanced with the risks that are associated with being so tightly digitally connected. The consequences of a breach occurring when companies are so connected can be akin to the “butterfly effect”. Where what may initially appear a small insignificant event in a non-descript supplier can manifest itself many times larger and more damaging somewhere else.
Why we now need to look beyond our perimeters?
My close colleague and well-respected expert Justin Leary uses the analogy of how medieval Knights used to defend themselves in their castles to how modern companies defend themselves from the threat of cyber-attacks. Both invest in developing the most effective defensive mechanisms and measures they can afford. The only difference being one was using bricks and mortar and now the other software. However, the real test of their resilience is when an enemy (invisible or not) lays siege to the castle. This resilience, or survivability shifts from one’s defensive capabilities to maintaining essential supply chains. These vulnerable channels which deliver much needed supplies to the castle are the Knight’s weakest link. Which if disrupted can see the strongest capitulated without an arrow or bullet being fired. Today, companies that can maintain strong defences whilst sustaining strong and predictable supply chains in an environment of persistent cyber threats, is in a strong position to thrive.
So, with every company investing as much as it possibly can into making themselves ever “harder targets” to penetrate, their greatest weakness has become their suppliers. These smaller companies tend to be less well-resourced but with whom they are highly interconnected.
Events of the past year concerning Covid are well documented, but there are other themes that are likely to be just as profound.
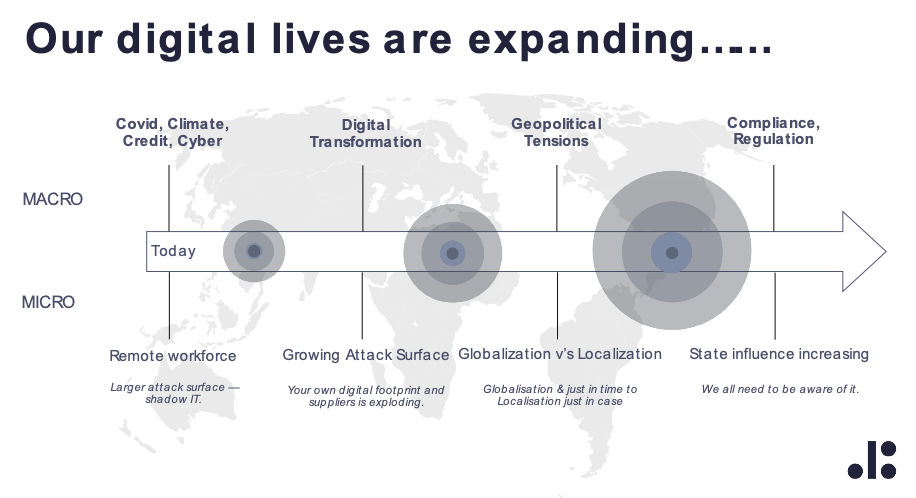
From managing the security of a remote workforce to an even larger and more complex connected supply chain, a company’s capability to be able to continuously monitor these numerous vulnerabilities and events beyond their perimeter has never been greater.
However, the task of doing this with traditional methods is close to impossible. Digital risk is persistent and disregards all conventions. No sooner do teams implement a solution that addresses a known threat it mutates presenting them with yet another variant. It is relentless. Yet procurement managers who are already managing a vast number of other equally demanding responsibilities across tens of thousands of suppliers are now faced with how best to include a digital risk monitoring capability. To achieve this, businesses require to implement non burdensome but effective systems and processes that align and seamlessly integrate with their other supplier compliance and governance responsibilities and applications. Enabling procurement to continually assess not just the digital risk of the supplier but the associated interdependencies that their operations and customers may have indirectly through this relationship.
To date that was easier said than done but with new digital risk data services that can be integrated with existing procurement and third-party risk platforms this capability is now accessible to all companies.
Prepare well - Putting the basics in place
At the very least, organisations should ensure that they are able to monitor the digital risk posture of all their suppliers and have basic controls, alerts, and thresholds in place.
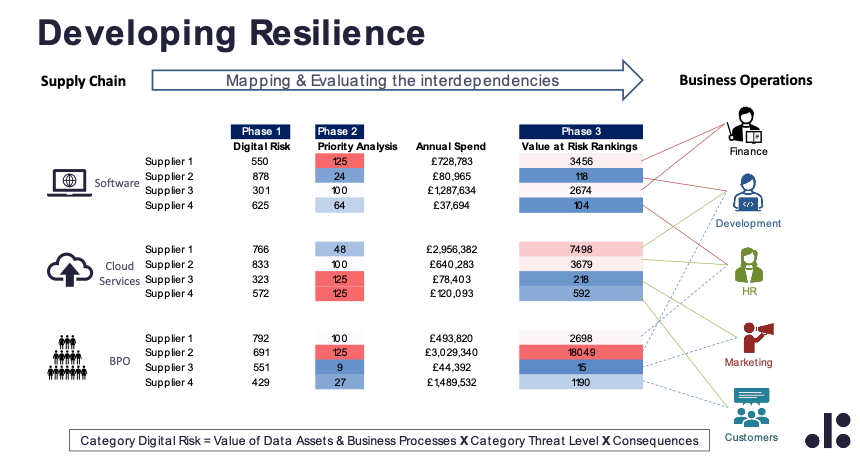
Once this first step is in place there will be a large amount of useful actionable data which requires to be prioritised. To achieve this, a useful exercise is to undertake a category digital risk analysis like the one below. This provides professionals a robust priority matrix from which they can structure their categories and direct their focus.
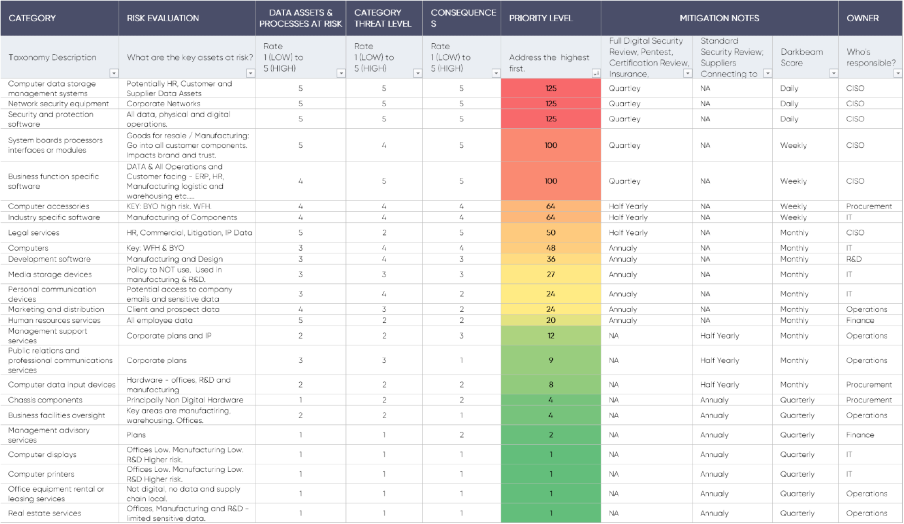
This data provides you a valuable view of each supplier through the “eyes of a bad-actor”. However, this outside-in perspective needs to be balanced by information and reassurances of the suppliers’ internal defence capabilities and data management controls. Furthermore, as well as effective processes, employees in the suppliers play an important role in helping to minimise risk. Digital security training should be included in the compliance vetting of suppliers so that employees in the suppliers are aware of the signs of vulnerabilities and how to spot threats and what do in the event of a breach. By integrating this into the existing risk and supplier information monitoring, logging and reviews, will ease the burden and stream-line digital risk with procurements other monitoring, compliance and reporting requirements.
Outlook
Many of the recent well-publicized supply chain attacks have been nation state orchestrated. However, if history rhymes then this style of attack will be adopted by well organised criminal gangs whose sole objective is financial gain. They will use the terrible threat of business disruption to extort. Prior to the broad adoption of crypto currencies and its associated characteristics of anonymity and traceability, it was hard for even the most skilled bad-actor to gain financially. That has significantly changed in their favour and a successful breach can now earn hackers staggering sums of money. Thereby, attracting an ever-increasing number of opportunists. In conclusion, the priority of 2021 and beyond is to embed digital risk into procurement’s risk management capabilities which will help us remove the opportunity for bad-actors to exploit and enable us to maintain healthy supply chains, so our businesses continue to serve our customers with ever better products and services.