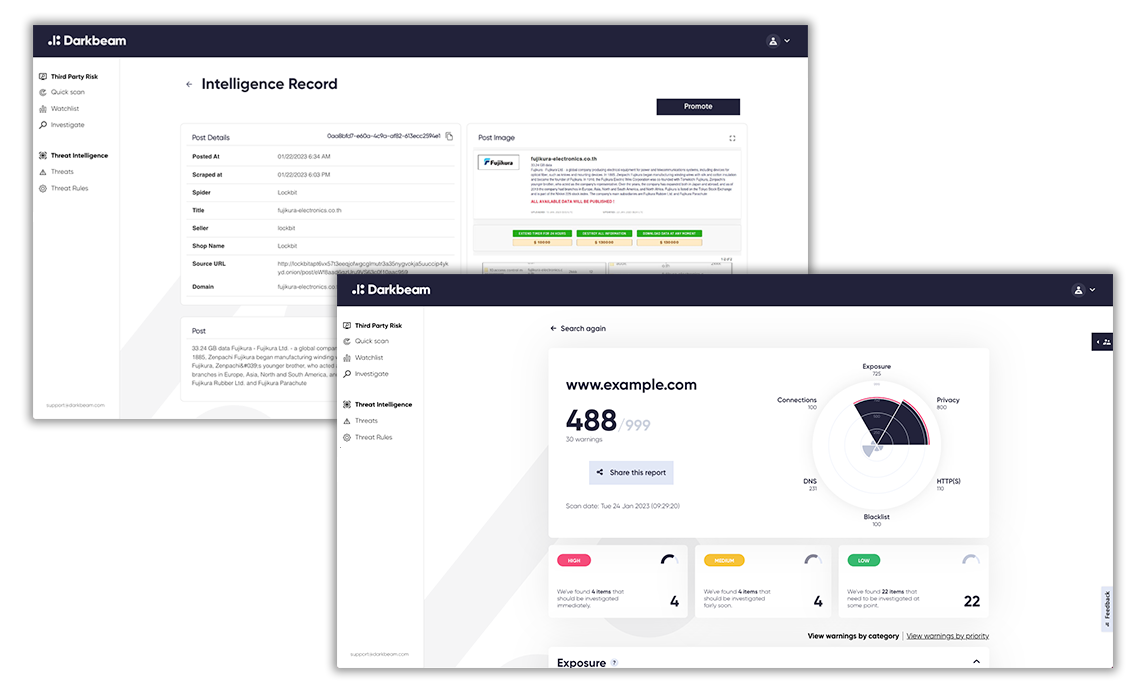
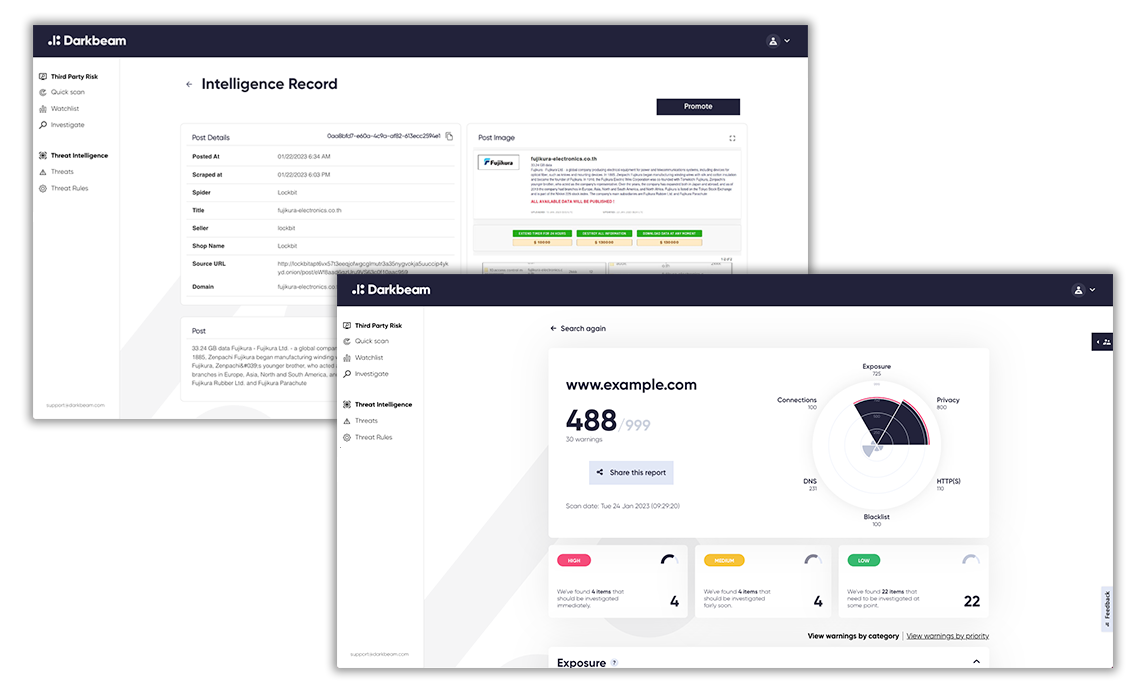
Predict, prevent and detect cyber threats in the supply chain with one automated platform. Darkbeam illuminates cyber risks among suppliers, pinpointing vulnerabilities, guiding responses, and notifying you of incidents that could jeopardise your business and reputation.
It takes your suppliers 207 days to discover a breach (on average) then 70 days to contain it. By then, sensitive data has been shared or critical operations disrupted.
With Darkbeam, it all takes less than an hour.
Don't let your supply chain be a black hole of cyber risk. Shine a light on threats in real-time with Supplier Threat Intelligence from Darkbeam.
Cyril Pourrat,
Chief Procurement Officer, BT & Chairman, BT Sourced

Gain instant visibility into the risk level of any supplier, access detailed risk reports and automate your monitoring for free.
Your Darkbeam account gives you visibility into your suppliers' cyber risk levels in a click. No manual forms and no expertise required.
Sign up for free. No credit card required.
Cyber incidents cause 50% of all supply chain disruption. But Supplier Cyber Risk Management is seen as a significant challenge for Procurement teams of all sizes.
With Darkbeam's combined Vulnerability and Threat monitoring, you don't need in-house experts. Darkbeam lets you assess and measure cyber risk across all suppliers in a click, automate ongoing monitoring and monitor the dark web for incidents affecting critical suppliers.
When we discover a supplier breach, our team will perform an immediate analysis, sending you an understandable, actionable report and guidance on approaching the supplier. Protect your business and reputation without an in-house cyber expert.
Your business's supply chain doesn't need to be a black hole of concern for cyber risk. Not only can Darkbeam's platform give you risk visibility for every supplier, it can also alert you when critical suppliers are breached.
We go way beyond data-dumps and credential breaches. Our platform continuously indexes dark web sites frequented by cyber criminals, generating data on emerging attacks against businesses, ongoing ransom activity and subsequent sale of data.
Unlike a 'firehose' data feed, we don't drown your team with pages of alerts requiring triage. Our platform and Analysts identify the intelligence you need and place it at your fingertips. So you gain the operational confidence and procedural governance to keep your team on the front foot.

Darkbeam is a London-based supply chain intelligence capability provider. Fuelled by innovations from Darkbeam Labs, our platforms make Cyber Risk Management accessible to Cybersecurity and Procurement teams of all sizes.
When you work with Darkbeam, you gain more than a vendor or software platform. We approach every relationship as a true partnership. You'll benefit from our team's years of cybersecurity expertise gained at the top of Government and Business, helping to strengthen your strategic governance and practical risk management from day 1.