A cyber attack against a single computer within a fence manufacturer has resulted in thousands of pages of sensitive information - including details of British military and intelligence sites - being leaked on the dark web.

This attack is another example of seemingly low-risk suppliers being compromised, leading to major data breaches. In this case, security information relating to sites including a nuclear submarine base, a chemical weapons laboratory and a GCHQ listening post were all released.
Lockbit – the Russian ransomware gang behind the attack – also stole information about high security prisons and another military base from the supplier.
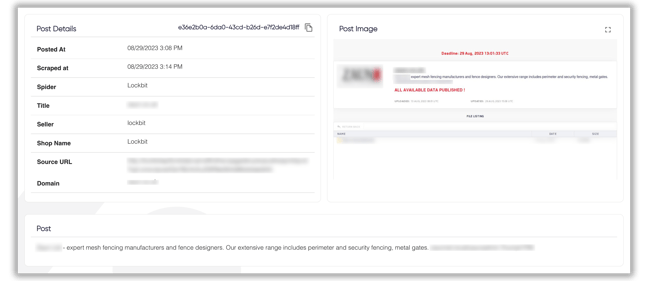
The data breach was detected and shown in Darkbeam's platform
One computer within one supplier was breached
As cyber attacks among suppliers become increasingly high-profile and damaging, organisations must learn from incidents such as this one. In this case, all of the stolen information was taken from a single ‘rogue windows 7 PC’ within a company who provided fencing to the sites.
Accessing that one computer allowed Lockbit to steal and release sensitive information with the potential to impact national security. The incident is being investigated by Britain's National Cyber Security Centre (NCSC).
Cyber criminals are prolific – this is not an isolated incident
While most organisations don’t need to protect security details relating to the home of Britain’s Trident nuclear programme, groups such as Lockbit (who carried out this attack) compromise and steal from companies every day.
Suppliers are attacked by intelligent, professional cyber criminals
This attack and subsequent data breach was carried out by an affiliate Lockbit. Lockbit itself is a company of Russian-speaking programmers who create software used by cyber criminals to extort and steal from organisations.
These criminals pay Lockbit to use their software and service - which includes the encryption tools, ransom negotiation and payments processing. If a company pays a ransom, access to their systems is restored, Lockbit does not release their data and the 'affiliate' takes 75% of the ransom that is paid.
Lockbit are very skilled and highly professional - they are operated like any other company. They are not alone in acting this way - ransomware groups are behind a very large percentage of high-profile cyber attacks.
We monitor Lockbit among many other ransomware groups as part of our Supplier Threat Intelligence capabilities. This article is being written on the morning of September 5th 2023 and we have already uncovered the details of 17 successful attacks by Lockbit against companies so far today.
Companies they have targeted today include a lawyer for military veterans, a food and beverage company, an architecture firm, a global logistics firm, a hospitality company, a college, a consulting firm, a gas company and more.
Cyber attacks against suppliers are a serious business risk
The regulatory impact (financial penalties), operational disruption, loss of reputation and potential for fraud caused when a supplier is attacked presents a serious business risk. Just as companies regularly assess and monitor suppliers’ credit-worthiness or ESG considerations, cyber risk must be monitored as a priority.
Despite this, very few companies (only 13% in the UK) engage in Supplier Cyber Risk Management activities. A key consideration for this is the perceived cost of the tools required and staff to manage them.
Darkbeam negates these issues by providing a highly cost-effective solution to monitoring vulnerabilities among entire supplier chains and detecting incidents among critical suppliers.
Try Darkbeam’s platform for free or contact us below to understand how our dual-capability supplier vulnerability and threat monitoring technology helps organisations of all sizes (from 10 suppliers to 30,000) measure, monitor and manage their exposure to cybersecurity risks within their supply chain.